 Criminals love chaos. During the cover of chaos, threat actors move in silence and attack, extract and demand ransom. Since the start of the pandemic, threat actors have enjoyed the turbulent landscape we’ve all been dealing with. Meanwhile, IT professionals are busy reconfiguring and standing up new networks, policies, practices, machines and training to enable a distributed workforce across a threat landscape that is stretching thinner and thinner. As this threat landscape flattens out, networks and systems will either tear or be reinforced.
Criminals love chaos. During the cover of chaos, threat actors move in silence and attack, extract and demand ransom. Since the start of the pandemic, threat actors have enjoyed the turbulent landscape we’ve all been dealing with. Meanwhile, IT professionals are busy reconfiguring and standing up new networks, policies, practices, machines and training to enable a distributed workforce across a threat landscape that is stretching thinner and thinner. As this threat landscape flattens out, networks and systems will either tear or be reinforced.
Cybercriminals looking for punctures in IT infrastructure don’t have to look too hard. Many IT orgs fail to execute on basic best practices such as updating firmware on firewalls and routers, let alone providing social engineering and IT security best practices training to their staff.
The National Institute of Standards and Technology (NIST) Cybersecurity Framework provides a starting point for IT pros looking to bolster their safety. The five core functions, as shown in Figure 1 below, provide a strategic view of the lifecycle of an organization’s cybersecurity risk management and should be treated as a key reference point.
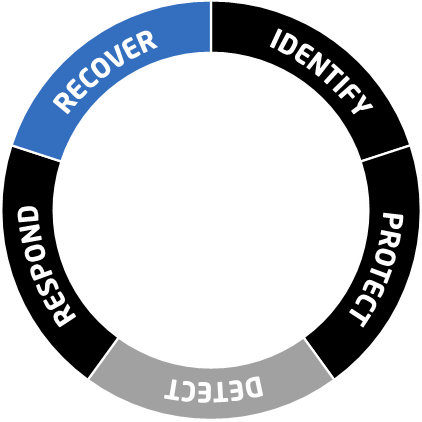
Figure 1: 5 core functions of the NIST Cybersecurity Framework
Let’s dig into each of these five functions and outline what types of tools can be added to an InfoSec or IT professional’s arsenal to defend themselves and their organizations.
#1 Identify
Before you can take action, you must know what you’re up against. To comply with this function, organizations need full visibility of both their digital and physical assets through reconnaissance. This visibility leads to understanding current risks and exposure, which then leads to putting measures in place to properly manage them.
There are several techniques IT pros can use to go about this:
- Asset Discovery Solutions
- Risk Assessments and Security Assessments
- Vulnerability Management Solutions
- Penetration Tests
Advantages of Using Asset Discovery Solutions
Visibility is a key component of any IT security practice – if you can’t see what’s going on, you’re going to be oblivious. Asset discovery solutions provide a complete and accurate inventory of your IT assets regardless of whether they are hosted in the cloud or located on-premises. It’s kind of like having a single pane of glass (or dashboard) to view all of the assets across the threat landscape. Using this method, you can view policies per asset, firmware versions, user actions that weaken the security profile and more. If a breach is isolated to a specific operating system, directory or manufacturer, you’re able to easily look up all of these assets and know when and where to triage effectively.
Advantages of Using Risk Assessments and Security Assessments
No matter how weak or strong your existing security posture is, there are going to be gaps. A security assessment is designed to help identify gaps so something can be done about them before they become a problem. It’s worth noting that best practice here is to use a combination of vendors to conduct your security assessment. Different vendors look at different databases and also have their own practice strengths in terms of the remediation they can offer in-house versus external. As you can imagine, they will focus more on what they can fix themselves post-assessment. That said, it’s important to implement some diversity here from different security firms a few times a year (or more depending on your compliance requirements).
Advantages of Using Vulnerability Management Solutions
These solutions search for unsecure system configurations, such as two systems communicating with one another when there is no real direct need for it. Another example would be patch management – these solutions will alert you when signatures are outdated. Keep in mind these tools are really scans, so there still has to be an actual InfoSec professional to hop in and make all the changes recommended by the vulnerability management solution provider.
Advantages of Using Penetration Tests
A white-hat hacker hacks into your systems and provides a detailed report on where they broke in, how far they got and what sort of passive data capturing malware they would have planted if they were an actual black-hat hacker. Again, it’s important to rotate hackers with this practice. Each hacker has their own specialties and techniques, and you want to make sure you are purposely exposing yourself to diversity of thought.
#2 Protect
If step one was, in essence, reconnaissance, step two is where the action happens. Once your organization knows where its risks and vulnerabilities lie, it’s time to implement the appropriate safeguards to prevent or limit the impact of a cyber attack.
Protection of assets isn’t a one-stop-shop. There are many angles to consider, namely:
- End Point Protection
- Email/Spam Filtering
- End User Awareness and Phishing Training
- Zero Trust Secure Remote Access
- Managed Intrusion Detection and Intrusion Prevention Systems
Implementing End Point Protection
Simply put, end point protection is anti-virus and malware protection. This is probably the most common cybersecurity solution found within most IT shops. However, it’s not a silver bullet. It’s a reactive solution that is limited by the integrity of the database that it draws from. It also doesn’t offer up a plan if or when a breach occurs.
Implementing Email and Spam Filtering
Email and spam filtering services are typically paired with a firewall. Best practice in 2021 is to have a hosted firewall to enable greater scalability and change management within the platform as your organization changes and morphs.
Implementing End-User Awareness and Phishing Training
End-user training is single handedly the most important investment and organization can make. Social engineering and phishing scams account for the massive majority of breach incidents during the pandemic. When you combine an uneducated end user that can’t decipher what a malicious email looks like with an extended attack surface, you have a recipe for disaster.
Implementing Zero Trust Secure Remote Access
This is one of the most innovative and interesting frameworks that is a part of NIST. The value in zero trust is that protocols, regulations and access privileges will change based on the location of the end point and who is accessing it. The same individual will have different access privileges on their home network, their corporate network or public Wi-Fi. These policies help force employees onto the encrypted infrastructure in order to access certain systems or directories. Cloud-based proxies regulate where and whether users are allowed to get to certain places.
Implementing Managed Intrusion Detection and Intrusion Prevention Systems
An intrusion detection system (IDS) monitors your network traffic and alerts you when something in the signatures looks like an attack. An intrusion prevention system (IPS) does the same thing while also classifying the traffic. IPS halts the traffic until whomever is managing the IPS goes in and opens it back up. This reactive approach is great, but it does suffer from false positives that can affect the users accessing the systems.
#3 Detect
Despite best efforts, cyberattacks of some magnitude are imminent. When they happen, how quickly your organization responds is critical. This means constant monitoring and threat hunting is par for the course.
There are a few tried and true methods of monitoring threats:
- Managed Detection and Response (MDR)
- Managed Security Operations Center as a Service (SOCaaS)
- Secure Access Service Edge (SASE)
Deploying Managed Detection and Response (MDR)
MDR is an outsourced security service that involves a tactical response team to hunt down and neutralize threats. One thing to keep in mind here is that a lot of vendors automate this process versus having responsive professionals who go in and handle the breach. A combination of both approaches is ideal. The key factor here is the contextual ability to intake the threat and decide in real time what sort of response push is necessary – knowing what systems and users need to be isolated, locked out or watched intently is not something that can be “set and forget.” MDR usually also involves endpoint detection and response (EDR). After all, end points are the start points for breaches.
Deploying Managed Security Operations Center as a Service (SOCaaS)
SOC as a Service augmentation might be the best fit for an organization that prefers to focus on their core business versus building an internal security team. A liaison within the organization can lead the Managed SOCaaS team to right incident response outcomes sensitive to business goals. This approach allows mid-sized organizations a “follow the sun” security response model as they gain 24/7 coverage.
Deploying Secure Access Service Edge (SASE)
SASE stands for secure access service edge. This is more of a methodology as opposed to a protocol or language of delivery. SASE takes the zero-trust methodology and takes it to the next level. Software-defined wide area networking (SDWAN), firewall as a service (FWaaS), cloud access service brokers (CASB) and secure web gateways (SWG) are all included services within a SASE offering. SASE gives organizations a contextual and intelligent real-time decision tree of security protocols and actions to take. Since it is an approach and not a box off the shelf, it makes it harder to peel open once the attack initiates.
#4 Respond
If a cyberattack happens, how you handle the impact matters. To comply, you must have an incident response plan that clearly defines communication across specific stakeholders, gathers and analyzes information about the attack, works to eliminate the threat and then follows up with lessons learned.
Organizations should have the following measures in place, just in case:
- Incident Response Teams
- Cryptocurrency
Create Incident Response Teams
Incident response teams typically involve a bit more than the 24/7 “follow the sun” SOC model in that they offer boots on the group services. These professionals will deploy themselves to your network environment to conduct a thoughtful forensic investigation mid-ransomware incident. Incident response teams can coach you and your team through a breach involving press relations, ransomware negotiation as well as dirty detective work.
Create a Crypto Wallet
Sometimes executives laugh when I bring this up, but I believe all businesses that have sophisticated IT assets need to have familiarity with cryptocurrency. A basic set up would involve creating a crypto wallet and having a small amount of Bitcoin (BTC) or Etherium (ETH) on hand. In the event of a breach, if you already have a crypto wallet, you will be able to focus on your IT assets versus figuring out how to create a digital crypto wallet. Every second counts. Think of this as being your belt wallet while you are traveling abroad. You don’t want to get caught in a bad situation that was made even worse due to your lack of preparation.
#5 Recover
After an injury, humans need to recover. Your security posture needs the same care and attention. Your recovery plan should obviously include restoration activities, but also needs to include updates via the lessons learned.
Include these best practices in your recovery plan:
- Incident Response Plan Assessment
- Business Continuity Disaster Recovery Assessment
- Digital Insurance
Include an Incident Response Plan Assessment
Building an incident response plan is ideally something that is done at the very start of your cybersecurity journey. But it’s during this phase of the NIST framework that you’ll actually be putting that plan into action. You can find boilerplates for this type of plan online, but make sure you are socializing it and customizing it with the various business leaders within your organization.
Include a Business Continuity Disaster Recovery Assessment
IT services are only one component of a business continuity and disaster recovery plan. This is being listed out separately from incident response simply because there are more facets to a recovery than getting IT systems up and running. Similar to the incident response plan, this is something that should be created earlier on in the process but will not actually be addressed until there is some sort of moment to breath and conduct a post-mortem regarding the attack.
Include Digital Insurance
Digital insurance is not a necessity for all industries, but it is certainly something you should consider regardless of your compliance requirements or business size. Having this insurance can soften the financial blow of recovering from a breach, as you may have to extend your bench to outside firms, replace technology or build a newly segmented environment from scratch as a result of your investigation.
The NIST framework is a helpful framework, but it lacks the detail necessary to steer an IT professional to the types of services and solutions they should invest in to get the circle completed. Hopefully this more detailed explanation has given you some perspective on what types of tools you can begin to do some preliminary research on in order to bring a more secure posture to your organization. You can learn these skills and more about the NIST Cybersecurity Framework in the CompTIA Cybersecurity Career Pathway.
CompTIA is here to support you throughout your IT career. Get free resources, career advice, and special offers on CompTIA training and certifications!

