
Cybersecurity has gone through some changes over the past decade. As organizations have dramatically increased their digital capabilities, they have also increased their potential vulnerabilities. Unfortunately, there hasn’t always been a direct connection between digital transformation and cybersecurity improvement. The IT team may understand how things are changing, but they need to be able to explain these changes to decision makers to build the best policies and determine the level of investment.
3 Issues Driving Cybersecurity Today
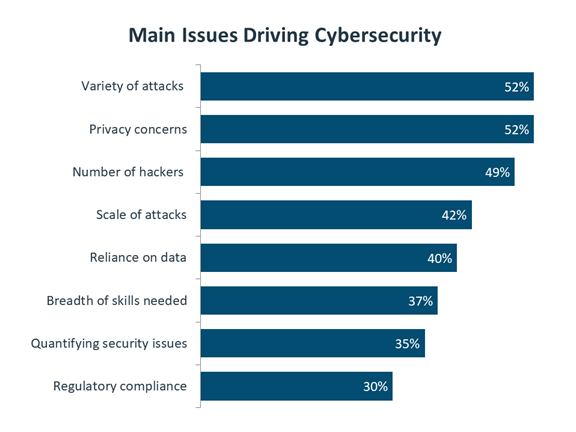
The data from CompTIA’s new State of Cybersecurity 2020 research report can help IT pros facilitate these conversations as their companies respond to a changing environment. Whether organizations are reacting to the COVID-19 pandemic or taking actions as part of a long-term strategy, the main issues driving cybersecurity can shape the decisions made by upper management.
An Increasing Attack Landscape
Organizations in CompTIA’s survey cited attack concerns as three of the top four issues driving cybersecurity today. The variety of attacks, the number of hackers and the scale of attacks are all top of mind for business executives and security professionals. However, business professionals may not truly understand the way that these issues are different from the past.
IT pros can help upper management realize the need for a new approach rather than simply enhancing existing defenses.
- Wider variety in attacks means that standard tools such as firewall and antivirus are no longer sufficient.
- More hackers means that attacks are happening for every company in every industry, not just major players.
- The scale of attacks means that a security breach can severely disrupt operations instead of being a minor annoyance.
These additional details, along with any metrics to back up the argument, can help make cybersecurity attacks more tangible for the business side of the house and support IT’s recommendations to increase cybersecurity efforts.
Privacy Concerns
The remaining issue in the top four is privacy. Privacy has certainly become a loaded topic, especially among consumers. Anyone operating in a business-to-consumer (B2C) environment has likely had a lot of discussions about how to guard their customers’ privacy. The issue is not as simple as turning on the privacy switch, though.
The problem is that it’s hard to have data privacy while also providing data-driven personalization. Consumers (and other business partners) may be delighted by highly personalized services without fully realizing that those services rely on data being shared.
The main issue is transparency, with the companies that provide services describing exactly how data is being used and taking care to only use the data needed for the service they are providing. IT pros can help their management understand the nuances of this situation and build appropriate messaging and processes.
Reliance on Data
Although privacy has become a hot button, customer data is not usually the most critical data in an organization. As businesses become more digital, they are relying more and more on data to support their operation. From finance to HR to product development, all types of data are critical, forcing companies to think beyond the most valuable intellectual property.
Just like with privacy, IT pros can highlight the new way of thinking about corporate data. The first new mindset is recognizing that data doesn’t stay in one place. That was the situation for years, which led to a strong focus on secure perimeter. Today, data travels everywhere, thanks to cloud and mobile and new tools are needed.
The second big shift is thinking about how the data gets used, rather than just assuming that all data has equal value. This leads to a more formal risk analysis process and a more granular approach for each data set.
Proposing Solutions for the Zero Trust Environment
By describing all these differences, IT pros can hopefully convince decision makers that modern cybersecurity requires a new way of thinking. If the old mindset was based on a secure perimeter, the new mindset is based on zero trust. Once management understands the problem, it is time to follow up with solutions.
The New Approach
First, IT pros should emphasize that there is a three-pronged approach to security. There are still technology tools being used, with the toolbox expanding beyond firewall/AV to include things like data loss prevention (DLP), identity access and management (IAM) and security information and event monitoring (SIEM).
Beyond the technology, companies should build process in areas like risk analysis and compliance management. Finally, they should focus on education that will improve security awareness for the entire workforce.
The Right People
The second part of a solution is to build the right team. With security becoming so complex, few organizations can afford to bring in experts in every area. Instead, companies will focus on a security operations center (SOC) with the most critical resources, then leverage outside firms for additional security expertise.
The Right Metrics
The last major piece of a security strategy is building metrics to track status. In the old days, success with cybersecurity was binary: Companies either experienced a breach or they didn’t (or at least they didn’t think so).
As the level of investment increases, executives will want to better understand what they are getting in return. Security professionals should build a standard set of metrics for demonstrating progress, such as the number of systems with up-to-date patching or the amount of network traffic flagged as suspicious.
The security landscape is very different than it was 10 years ago, and it is always changing. IT pros have an opportunity to drive the security discussions within their organization, and staying up to speed on the latest trends will help with that mission.
How CompTIA Certifications Keep You Up to Date
CompTIA cybersecurity certifications help you stay on top of the latest cybersecurity threats and how to combat them. With updates every three years, you can be certain that by getting a CompTIA cybersecurity certification, you’re validating the skills needed in today’s cybersecurity environment.
The CompTIA Cybersecurity Career Pathway has four certifications geared toward IT pros with different levels of experience:
- CompTIA Security+ is designed for those with two years of IT administration experience with a security focus
- CompTIA Cybersecurity Analyst (CySA+) covers defensive cybersecurity skills and is designed for those with at least 4 years of hands-on information security or related experience
- CompTIA PenTest+ covers offensive cybersecurity skills and is designed for those with at least 3-4 years of hands-on information security or related experience
- CompTIA Advanced Security Practitioner (CASP+) is designed for those with at least 10 years of IT administration experience and at least 5 years of hands-on technical security experience
Whether you’re just getting into cybersecurity or at the top of your game, CompTIA certifications help you keep your knowledge and skills up-to-date.
Download the exam objectives for CompTIA certifications for free to see what’s covered and start studying.

