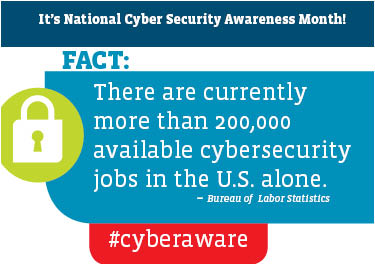
 In the current, complicated cybersecurity landscape, there’s no one solution or platform that can keep an enterprise or institution safe on its own. Preventing cyber attacks takes knowledgeable, talented IT security staff. So if you’re interested in focusing on this critical side of the IT field, there is a ton to learn – and a ton of opportunity.
In the current, complicated cybersecurity landscape, there’s no one solution or platform that can keep an enterprise or institution safe on its own. Preventing cyber attacks takes knowledgeable, talented IT security staff. So if you’re interested in focusing on this critical side of the IT field, there is a ton to learn – and a ton of opportunity.
But what sort of jobs are out there and what do you need to know to handle them? Though necessary skills, responsibilities and titles can always vary depending on workplace needs, size and organizational hierarchy, this run-through of positions should give you a good starting point for understanding what the job prospects look like, and how far you can go, in the world of cybersecurity.
-
Security Administrator: A security administrator position is generally considered the first rung on the cybersecurity ladder, and though it is “entry-level” in the cybersecurity field, that doesn’t mean it’s non-technical. Quite the opposite. The expectation include managing security solutions, doing basic network monitoring, making sure patches get rolled out and doing all the other ground-level security work in an office. This is a position that Security+ sets you up to succeed in.
- Security Specialist: The next step up the enterprise hierarchy is usually a specialist. Like someone who moves from the associate to the manager level in a non-tech career, this role is a step up in responsibility, generally requiring delegating responsibility to a team while taking on higher-level management of tech tools, and offering more advisement in and outside of the IT department.
- Information Assurance Technician/Specialist (and Other Military-related Roles): In the military cybersecurity is a top priority, but job titles are different from what you might see in the civilian world. Different tiers of Information Assurance Technician job require specific certifications to meet the Department of Defense’s criteria to work on secure networks. In lower-level roles, Security+ is a must. In higher-level roles, the tough and technical CompTIA Advanced Security Practitioner (CASP) exam is required. Even if you’re non-military, if you find yourself working in consulting on a military contract and are touching networks that require clearance to work on, it can make it a non-negotiable necessity to have these security certs on your resume.
- Security Analyst: The sheer volume of cybersecurity threats that have been proliferating on the enterprise landscape has been taxing the bandwidth of IT professionals. This has led to the advent of new, higher-level network monitoring and analytics tools critical to determining how a network could be compromised and how to respond to the threat. Security analysts are the people inside an enterprise who can manage SEIM tools, threat intelligence platforms and other such tools, understanding the complicated log files they generate and putting them in context to inform action. This role is becoming so important, in fact, that CompTIA is launching a brand new certification, the Cybersecurity Analyst+ (CySA+), to set the benchmark for what someone in this role needs to know.
- Senior Cybersecurity Engineer/Architect: Cybersecurity threats have grown not just in number, but in sophistication. To keep invaders out, a business needs people who understand what’s happening on networks, servers and databases at the most sophisticated levels and can secure every facet accordingly. This the role of the engineer/architect. For IT pros at this level, the CASP is the certification that proves they’ve got what it takes.
Matthew Stern is a freelance writer based in Chicago who covers information technology, retail and various other topics and industries.

