
One of the first things I remember doing as a kid was writing secret messages to friends using invisible ink. I was only about 8 or 9 at the time, so I used the tools my mom unwittingly made available: Lemon juice and an iron. I wrote my secret message on a piece of paper and then told my friend to use an iron or even a match – some sort of heat source – to burn the lemon juice a bit, turning it brown. This revealed the secret message I wanted to share. Ever do that yourself? Well, if you have, you and I have engaged in the time-honored practice of steganography.
What is Steganography?
Steganography is the practice of hiding a secret message inside of (or even on top of) something that is not secret. That something can be just about anything you want. These days, many examples of steganography involve embedding a secret piece of text inside of a picture. Or hiding a secret message or script inside of a Word or Excel document.
The purpose of steganography is to conceal and deceive. It is a form of covert communication and can involve the use of any medium to hide messages. It’s not a form of cryptography, because it doesn’t involve scrambling data or using a key. Instead, it is a form of data hiding and can be executed in clever ways. Where cryptography is a science that largely enables privacy, steganography is a practice that enables secrecy – and deceit.
How Steganography is Used Today
Steganography has been used for centuries, but these days, hackers and IT pros have digitized it to do some pretty creative things. There are a number of apps that can be used for steganography, including Steghide, Xiao, Stegais and Concealment.
The word steganography seems fancy, but it actually comes from a fairly normal place. The root “steganos” is Greek for “hidden” or “covered,” and the root “graph” is Greek for “to write.” Put these words together, and you’ve got something close to “hidden writing” or “secret writing.”
Here’s an example of how digital steganography works. A friend of mine sent me a steganographic message – a secret message embedded within an image. The image was a photo that I had previously sent him of a geyser I had paddled to while on Yellowstone Lake last summer.

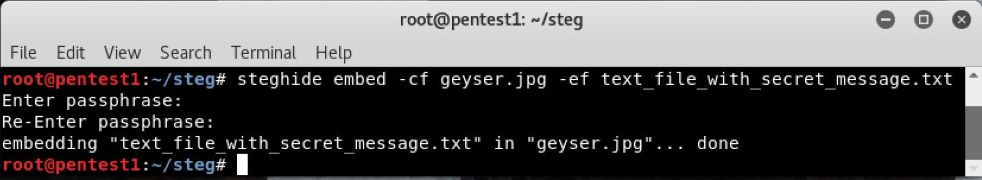
To embed his secret message to me, my friend then issued the commands shown in Figure 2.
With my own copy of Steghide (available in Windows, Linux and Mac), I used the command sequence shown in Figure 3 to extract that secret message. I then read it using the cat command.
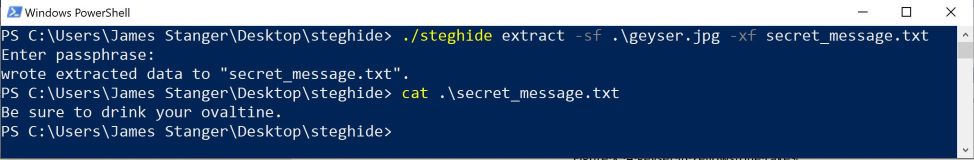
Apparently, my friend is a fan of the classic movie Christmas Story and somehow felt the need to repeat Little Orphan Annie’s reminder for us all to keep up with our nutrition: “Be sure to drink your Ovaltine.”
This is a trivial example of how steganography has been used over the decades. But over time, penetration testers and attackers alike have been using steganography to do more than share messages.
Using Steganography to Deliver Attacks
Today, attackers use PowerShell and BASH scripts to automate attacks. So are pen testers. For example, attackers have been embedding actual scripts within macro-enabled Excel and Word documents. Once a victim opens the Excel or Word doc, they activate the embedded, secret script.
The attacker doesn’t need to trick the user into using applications such as Steghide. In this case, the hacker – or pen tester – is “living off the land.” The attacker is using a steganographic application to take advantage of common Windows applications and features such as Excel and PowerShell. All the victim needs to do is read the doc, and an unfortunate series of events begins to occur.
- First, the victim clicks on an Excel document that an attacker has modified using steganography.
- That click unleashes a hidden PowerShell script.
- This script then installs an installer app into the Windows computer. This installer app moves quickly and is so subtle that typical antivirus applications don’t notice it.
- This downloader then goes out to the internet and grabs updated versions of malware such as URLZone (or more recent tools) that then compromise the victim’s computer.
Over the years, attackers have used the procedure above to deliver ransomware such as Snatch. Hackers have installed sophisticated malware that is cable of keylogging, enlisting computers into DDoS botnets or installing trojans, such as the latest variants of Rovnix and Pillowmint. The list goes on.
Artificial Intelligence and Steganography
We’re also seeing attackers add artificial intelligence (AI) into the mix. Increasingly, we’re seeing AI uses of various tactics, including steganography, to hide information. AI implementations have even been able to modify steganographic techniques so that attacks can’t be easily discovered.
Detecting Steganography
Security analysts work to identify the tactics, techniques and procedures (TTPs) of attackers and pen testers. Over the years, they have identified typical signatures that steganographic applications use. This is why antivirus applications, for example, can identify typical moves made by steganographic applications.
Therefore, pen testers and attackers morph and modify their procedures to thwart detection. And so the cat and mouse game continues: Attackers constantly modify tools and techniques, and security analysts constantly look for new signatures and methods.
CompTIA Cybersecurity Analyst (CySA+) validates the skills needed by cybersecurity analysts, including steganography. Download the exam objectives for free to see what skills you need to be a cybersecurity analyst.

