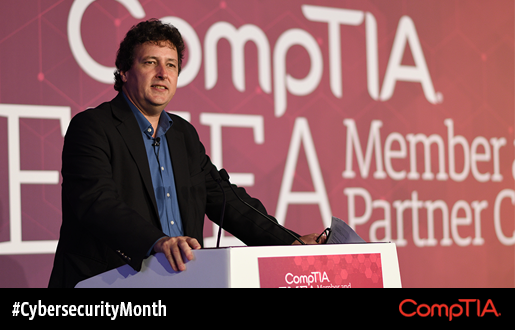
With technology changing and developing every day, it is vital that today’s cybersecurity professionals are able to adapt to evolving situations without getting too rooted in one focus, according to the Emerging Tech Smackdown session at EMEA Member and Partner Conference.
Dr. James Stanger, Chief Technology Evangelist at CompTIA, (pictured right), led the session with Chris Hodson, CISO EMEA of Tanium, and Gary Fildes, cybersecurity and information security principle inspector at the Office of Nuclear Regulation, covering everything from the myth of the cybersecurity “expert” to the new threats faced from technologies like the internet of things (IoT) and artificial intelligence (AI).
IoT is Everywhere
The internet of things might be the most problematic technology from a cybersecurity standpoint because it is becoming increasingly integrated into society. The extent of this was demonstrated when the speakers asked the audience at EMEA to hold up their fingers to show how many IP-enabled devices they had on them at that moment in time. The vast majority of attendees had at least two devices, with many people holding up three and even four fingers.
Stanger, Hodson and Fildes discussed how machines communicate about us as we move, meaning that data is constantly being created and stored about us, some of which can be used for malicious purposes. They predicted that in the future, our environments will customize themselves for us because of the data collected by the devices that are in our lives.
Humans vs. AI
The speakers also raised the question of the potential for AI to make deductive leaps or whether this is where humans should step in. Machine learning is a necessity today, and humans will never be able to operate as quickly alone. While AI can’t make the deductive leaps of humans—yet—it can identify patterns that can be useful for locating malware based on specific traits, such as in emails and data sets.
The speakers also debunked the myth that AI is taking jobs. “We will always need humans to make the decisions about which decisions AI will make,” said Hodson. Fildes agreed, saying businesses will need to invest as much in training employees as they do in adopting AI. However, with Amazon’s warehouses already almost exclusively manned by robots, the extent of the role humans will play in the future of work will depend on the industry and role in question.
Insecure Cybersecurity
One surprising discovery from the discussion of cybersecurity was that hacks are seasonal. Speakers warned that there is a rise of hacks in January after Christmas, once workers have returned to work and forgotten their passwords. Hodson revealed that Summer19 turned out to be a common password for employees who have returned from their holidays and reset their passwords—in other words, a hacker’s magic key.
But even with the high-profile data breaches we have witnessed this summer, businesses are investing heavily in the prevention of cyber breaches without considering how they would recover if they did suffer one. Without a tested recovery plan, businesses are setting themselves up for failure. The speakers equated it as being the same as investing significant amounts of money into your wedding day, then losing your wedding photos because they weren’t backed up.
Build Foundations Before Towers
While it was agreed that the role of cybersecurity ‘expert’ may be a myth, importance was placed on the ability to specialize in certain areas. When hiring or training staff to fill cybersecurity riles, focus on building the foundations of awareness, gain confidence in the basics and then specialize.

 Add CompTIA to your favorite RSS reader
Add CompTIA to your favorite RSS reader