Managed service providers (MSPs) and solution providers can agree on this—it’s been a busy year for managing customers’ cybersecurity needs. As the result of a global pandemic, MSPs helped customers move servers, other hardware, and applications off premise to the cloud. Solution providers scaled their ability to secure endpoints as more employees started working remotely. Secure platforms were in high demand as customer communications, collaborations and meetings went virtual.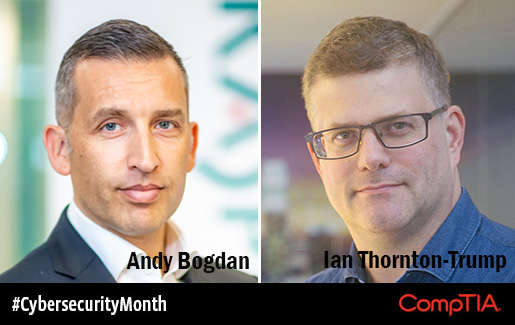
How have these shifts affected the cybersecurity threat landscape? What best practices can be applied going forward? Andy Bogdan, head of UK SMB Channel at Kaspersky, and Ian Thornton-Trump, chief information security officer at Cyjax, were among the cybersecurity experts that talked with MSP partners during a Genius Café session at a recent CompTIA UK Channel Community virtual meeting. Attendees sought security advice from the geniuses, who offered their best advice and strategies for success. Here, Bogdan and Thornton-Trump share their top takeaways from the conversations.
A Perfect Storm
The social and economic disruption resulting from COVID-19 created a perfect storm for malicious users to carry out attacks on enterprise and small to medium business (SMB) customers.
Smaller companies that lack basic security awareness and training are particularly vulnerable to breaches, hacks, and attacks, according to Bogdan. “Security awareness within organisations is the common denominator and weakness for many [SMBs]. There is still significant ignorance that they will not be targeted or affected by modern day cybercriminals. SMBs are more at risk than they have ever been,” he explained.
Old Tactics with a New Twist
Cybercriminals unleashed old tactics using COVID-19 themes:
- Phishing emails disguised as company, health, or government authorities
- Malicious domains that prey on the need for COVID-19 information or products
- Malware, including ransomware and distributed denial of service (DDoS) attacks, targeting healthcare providers
For many MSPs and solution providers, old excuses for not implementing cybersecurity measures no longer hold water. Thornton-Trump noted, “In 2015, in the early days of CryptoLocker [a type of ransomware], the common excuse was ‘This is new, this is sophisticated.’ In 2020, ransomware is neither new nor is it sophisticated. And it’s delivered the exact same way it was in 2015—usually by phishing email.”
Bogdan agreed, “With the reemergence of legacy threats, such as ransomware, and an increase in sophisticated phishing attacks, threat actors can leverage SMBs and remote workers as a steppingstone to seek out and penetrate enterprises.”
Configuration Oversights and Unpatched Vulnerabilities
In 2020, cybercriminals found fertile ground to exploit security configuration oversights as cloud collaboration services were hastily deployed following the pandemic.
Unpatched vulnerabilities in popular software applications were also common targets. In September, CompTIA’s Information Sharing and Analysis Organization (ISAO) alerted members of a privilege vulnerability in Microsoft’s Netlogon, a remote protocol that authenticates network users and machines. If unpatched, threat actors could use this vulnerability to obtain domain administrator access.
Actionable Steps to Mitigate Risk
Bogdan and Thornton-Trump shared actionable steps for MSPs and solution providers to shore up cybersecurity defenses and mitigate their risk.
1. Implement a multi-layered security approach.
A multi-layered security approach consists of separate components that, when working together, provide needed backups and coverage when facing attacks. Those components may include:
- Email security
- Antivirus software
- Web protection and filtering
- Vulnerability assessment
- Endpoint detection response
- Firewalls
- Privacy controls
- Data backups
- Patch management
2. Maximize your network protection.
Enterprise firewalls are expensive, and Thornton-Trump encouraged MSPs and solution providers to invest wisely, “I’m seeing too much old kit still in use that offers minimal network-level protections. We need to get real about what countries we are sending or receiving packets to and from against our exposed services.”
3. Enable network level authentication for remote control and users.
As the number of remote users soared in Q2 2020, so did the need for remote desktop protocol (RDP) and virtual private network (VPN) services. Network level authentication measures are key for limiting risk. “If you need RDP or VPN services into your network core, those services should not be available across the entire internet, and they should be protected with 2FA along with unique and robust passwords,” Thornton-Trump said.
4. Look for training programs to strengthen customer awareness.
Non-IT personnel at enterprise and SMB customers remain the greatest risk for cybercrime, particularly social engineering tactics. MSPs and solution providers should leverage security vendor training programs to bolster awareness of cybercrime, in all its forms.
Bogdan noted, “It’s the role of cybersecurity vendors like ourselves to lead the way with education from the board right down/across to the general users and technical teams, particularly within the SMB space.”
5. Access real-time threat intelligence feeds.
Stay up to date on critical cybersecurity threats by subscribing to threat intelligence feeds. Different repositories and tracking websites alert MSPs and solution providers to new vulnerabilities, exposures, and emerging threats.
For example, CompTIA’s ISAO combines actionable real-time threat analysis with access to a trusted network of industry peers for cybersecurity thought leadership and best practices.
6. Identify customers’ ability to analyze threat data.
Most cybersecurity vendors include endpoint detection and response (EDR) tools as part of their product suites. These tools monitor activity data and identify threat patterns, but threat data is pointless if end users don’t know how to analyze it.
Bogdan shared, “Many EDR solutions sold today are noisy visually, and general SMBs and small to medium enterprises (SMEs) don’t have the time or skills to monitor and analyse every alert they receive. The qualification question that’s not being asked of customers [is]—does the customer have the skills to analyse and explore/investigate the threat data?”
7. Report phishing, malware, and fraud.
MSPs, solution providers and customers should actively report cybercrime to software developers and security vendors. “Not enough people are reporting phishing emails, fraudulent websites and other internet-related fraud. We need to unleash hell every time a customer or our business gets attacked. The more reports that are made, the greater likelihood security vendors will update their products to provide protection for others. Go to this site and start doing this stuff. It can make a difference,” Thornton-Trump said.
Have You Registered for CompTIA’s EMEA Member and Partner Conference Online?
Don't forget to sign up now to attend the CompTIA EMEA Member and Partner Conference, a digital event scheduled for 13-14 October. Learn about the latest emerging technology trends and network with industry leaders.

 Add CompTIA to your favorite RSS reader
Add CompTIA to your favorite RSS reader

